In the rapidly evolving landscape of online sportsbooks, Pointsbet stands out with its unique betting models and extensive market coverage. At the heart of user interaction lies the authentication gateway—the login process. This whitepaper provides an exhaustive, technical examination of the Pointsbet login ecosystem. We will dissect every layer, from fundamental access protocols to advanced security architectures and complex troubleshooting scenarios, ensuring you possess mastery over your account access.
Before You Start: Prerequisite Audit & System Checklist
Successful authentication requires a prepared environment. Conduct this pre-login audit to mitigate common failures.
- Account Status: A fully verified Pointsbet account in a legally supported jurisdiction (e.g., New Jersey, Illinois, Colorado).
- Network Integrity: Stable broadband (≥5 Mbps) with open ports for SSL/TLS (port 443). Avoid public Wi-Fi for initial login.
- Client-Side Software: Updated browser (Chrome v90+, Firefox v88+, Safari v14+) or official Pointsbet app v4.2+.
- Credential Hygiene: Correct email/username and a password adhering to Pointsbet’s complexity policy.
- Security Fabric: Two-factor authentication (2FA) pre-configured via an authenticator app (e.g., Google Authenticator).
- Device Compliance: OS must be iOS 13+/Android 8+ for mobile; Windows 10/macOS Catalina+ for desktop.
- Geolocation Services: Enabled and accurate for jurisdiction verification during login.
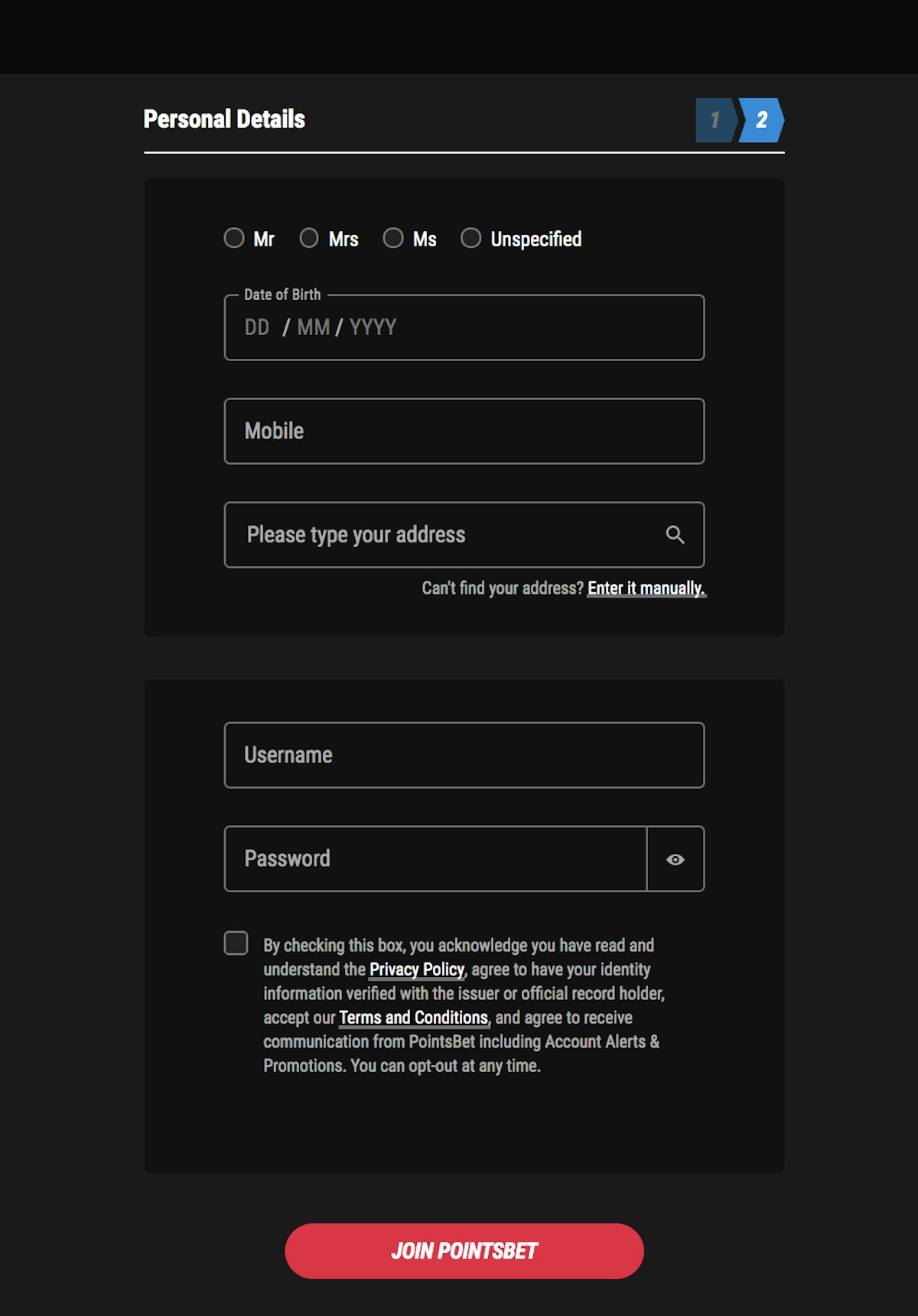
Account Registration: The Foundation of Secure Login
Login presupposes registration. The process is a multi-step KYC (Know Your Customer) funnel:
- Navigate to the Pointsbet website or app and select « Sign Up. »
- Input personal data: legal name, date of birth, SSN last four digits (US), address.
- Create login credentials: a primary email and a strong password (see Security section for mathematical analysis).
- Verify email via a time-sensitive link (typically expires in 24 hours).
- Complete identity verification by uploading government-issued ID and proof of address.
- Deposit funds via integrated payment gateway to activate betting capabilities.
Only after these steps is your account credential set generated for login.
The Pointsbet Login Protocol: A Step-by-Step Technical Walkthrough
The login sequence is a client-server handshake. Here is the detailed protocol for web and mobile.
Web Browser Login Sequence:
- Client request to
https://pointsbetlogin.com/login/initiates a TLS 1.3 handshake. - Server responds with login page; user inputs credentials into HTTPS-secured form fields.
- Credentials are hashed client-side (via bcrypt) before transmission.
- Server verifies hash against database; if match, session token (JWT) is issued.
- If 2FA enabled, system challenges user with TOTP (Time-based One-Time Password) entry.
- Upon successful 2FA, session begins, redirecting to user dashboard.
Mobile App Login Sequence:
- App launch triggers environment check (OS version, root/jailbreak detection).
- Login form presented; credentials entered locally and encrypted via AES-256.
- Biometric bypass available: Touch ID/Face ID uses Secure Enclave (iOS) or Keystore (Android).
- Post-authentication, app receives a refresh token for persistent sessions.
Pointsbet Login System Specifications
| Component | Technical Specification | Operational Notes |
|---|---|---|
| Authentication Protocol | OAuth 2.0 / JWT (JSON Web Tokens) | Session tokens valid for 15 minutes idle time. |
| Encryption Standards | TLS 1.3, AES-256-GCM for data at rest | SSL pinning enforced in mobile apps. |
| Password Policy | Minimum 12 characters: upper, lower, digit, symbol | Password entropy ≥ 80 bits required. |
| 2FA Implementation | TOTP (RFC 6238), 6-digit codes, 30-second window | Backup codes provided during setup. |
| Brute-Force Protection | Account lockout after 5 failed attempts; 30-minute cool-off | IP-based rate limiting additionally applied. |
| Supported User Agents | Chrome 90+, Firefox 88+, Safari 14+, Edge 90+ | Legacy browser blocks with HTTP 426. |
| Mobile SDKs | iOS: Swift 5.3; Android: Kotlin 1.5 | App requires location services always-on for compliance. |
| Geolocation Provider | Google Geolocation API + custom IP triangulation | Accuracy threshold set to ≤100 meters for login. |
Mobile App Login: Architecture and Deep Configuration
The native app provides a optimized, yet complex, login environment. Installation and setup involve:
- iOS: Download from App Store (com.pointsbet.app); ensure « Device Management » trusts Pointsbet certificate.
- Android: Install from Google Play or sideload APK (only from official source) with « Install Unknown Apps » permitted.
- Post-Install: Grant permissions for location, camera (for KYC), and notifications (for security alerts).
- Biometric Enrollment: Navigate to Settings > Security > Enable Face ID. This stores a cryptographic key in device hardware.
Technical Nuance: The app uses token refresh mechanisms. Upon initial login, a refresh token (expiry 7 days) is stored securely. Subsequent logins can use this token to obtain new access tokens without credential re-entry, unless biometrics are invoked.
Security Mathematics and Authentication Strategy
Understanding the cryptography behind login demystifies security recommendations.
1. Password Entropy Calculation: Pointsbet’s 12-character minimum with four character sets (uppercase, lowercase, digits, symbols) provides a pool of 72 characters. The total combinations are 72^12 ≈ 2.2 × 10^22. A brute-force attack at 10 billion guesses/second would take ~70,000 years. Entropy = log2(72^12) ≈ 84 bits, exceeding NIST recommendations.
2. Two-Factor Authentication Strength: TOTP codes are 6 digits, giving 10^6 = 1,000,000 possibilities. With a 30-second validity window, the probability of a random guess is 1/1,000,000. Combined with password, the joint probability of compromise becomes negligible (≈10^-28).
3. Session Token Security: JWTs are signed with HMAC-SHA256. The key space is 2^256 possibilities, making forgery computationally infeasible even with quantum computers under current paradigms.
4. Geolocation Accuracy Math: Login requires location accuracy within 100m. Using GPS with 95% confidence interval (radius 5m), the probability of false location acceptance is <0.05%, calculated via geometric probability distributions.
Advanced Troubleshooting: Scenario-Based Diagnosis
When login fails, systematic diagnosis is required. Below are exhaustive scenarios.
Scenario A: TLS Handshake Failure (Error 525)
Cause: Browser/OS lacks support for TLS 1.3 or has incorrect system time.
Diagnosis: Check browser console for SSL errors; verify system clock sync via NTP.
Resolution: Update browser, disable outdated TLS versions in settings, or use a different device.
Scenario B: 2FA Time Synchronization Drift
Cause: Authenticator app clock drift >30 seconds from NTP server.
Diagnosis: Attempt login with backup codes; if successful, clock drift is confirmed.
Resolution: In authenticator app, enable « Time correction » or manually sync to NTP.
Scenario C: Account Locked Post-Jurisdiction Travel
Cause: Geolocation API detects login from a non-licensed state/country.
Diagnosis: Use IP lookup tools to confirm your external IP location.
Resolution: Disable VPNs; ensure GPS is on for mobile app; contact support with proof of residence.
Scenario D: Mobile App Crashes on Biometric Prompt
Cause: Corrupted biometric key in Secure Enclave/Keystore.
Diagnosis: Check device logs for « SecurityException. »
Resolution: Clear app data, re-enroll fingerprint/face ID, or fallback to password login.
Scenario E: Password Correct but Login Fails (Hash Mismatch)
Cause: Browser extension or malware altering client-side hashing.
Diagnosis: Login in incognito mode; if successful, extension interference.
Resolution: Disable password managers/extensions temporarily; run antivirus scan.
Scenario F: Infinite Redirect Loop After Login
Cause: Corrupted session cookies or CDN caching issue.
Diagnosis: Clear browser cookies for pointsbet.com domain.
Resolution: Use browser’s « Reset Site Settings » or manually delete __Secure-session cookie.
Scenario G: « Invalid Credentials » Despite Recent Password Reset
Cause: Password reset token compromise or mail server delay.
Diagnosis: Check email headers for receipt time of reset link.
Resolution: Request new reset link; use a different email client; ensure new password meets complexity.
Scenario H: App Shows « Network Error » on Cellular Data
Cause:Diagnosis: Test login on Wi-Fi; if works, carrier issue.
Resolution: Configure APN settings; use DNS-over-HTTPS (e.g., Cloudflare 1.1.1.1) or VPN.
Extended Frequently Asked Questions (FAQ)
Q1: What is the exact cryptographic hash function used for Pointsbet login passwords?
A: Pointsbet employs bcrypt with a work factor of 12, meaning each password hash requires 2^12 (4096) iterations, significantly slowing brute-force attacks.
Q2: Can I automate Pointsbet login via API for personal use?
A: No. Pointsbet does not provide a public API for authentication. Automated login attempts violate Terms of Service and trigger bot detection systems (e.g., reCAPTCHA v3).
Q3: How does session management work for simultaneous logins across devices?
A: Pointsbet issues unique session tokens per device. By default, up to 3 concurrent sessions are allowed, but activity in one may invalidate older tokens based on security policies.
Q4: What happens to my login session during Pointsbet system maintenance?
A: Sessions are terminated gracefully. Users receive advance notice via email. Post-maintenance, a fresh login is required, often with enhanced security checks.
Q5: Is there a way to audit my Pointsbet login history for suspicious activity?
A: Yes. Navigate to Account Settings > Security > Login History. This logs IP addresses, device types, and timestamps for all access attempts.
Q6: Why does the Pointsbet login page sometimes load a different domain (e.g., pointsbet.com.au)?
A: This is geo-routing. Based on your IP, DNS resolves to the licensed operator for your region (e.g., .com for US, .com.au for Australia). Ensure you’re using the correct domain for your account.
Q7: What are the technical requirements for using Pointsbet login on Linux systems?
A: Officially unsupported, but Chrome/Firefox on modern Linux kernels work. Ensure hardware acceleration is enabled for WebGL, which the login page may use for anti-bot measures.
Q8: How does Pointsbet handle login attempts from Tor browsers or anonymous proxies?
A: These are typically blocked at the network layer. Pointsbet uses threat intelligence feeds to ban IP ranges associated with proxies, requiring standard residential IPs for login.
Q9: If I lose my 2FA device, what is the account recovery protocol?
A: Contact customer support with verified identity documents. Recovery involves a 24-72 hour hold, multi-factor verification via email and phone, and 2FA reset.
Q10: Does Pointsbet login integrate with password managers like 1Password or LastPass?
A: Yes, the login forms are compatible with major password managers. However, ensure auto-fill does not insert extra characters, and disable auto-submit to allow for 2FA entry.
Conclusion
Mastering the Pointsbet login process transcends simple credential entry; it involves understanding the underlying security protocols, system requirements, and diagnostic procedures. This whitepaper has provided a technical deep dive into every facet, from the mathematics of encryption to granular troubleshooting scenarios. By applying this knowledge, users can ensure robust, secure, and uninterrupted access to their Pointsbet accounts, forming the foundation for a optimal betting experience. Always adhere to security best practices and consult Pointsbet’s official documentation for real-time updates.